Difference between DOS and DDOS attacks
What Are DoS and DDoS Attacks?
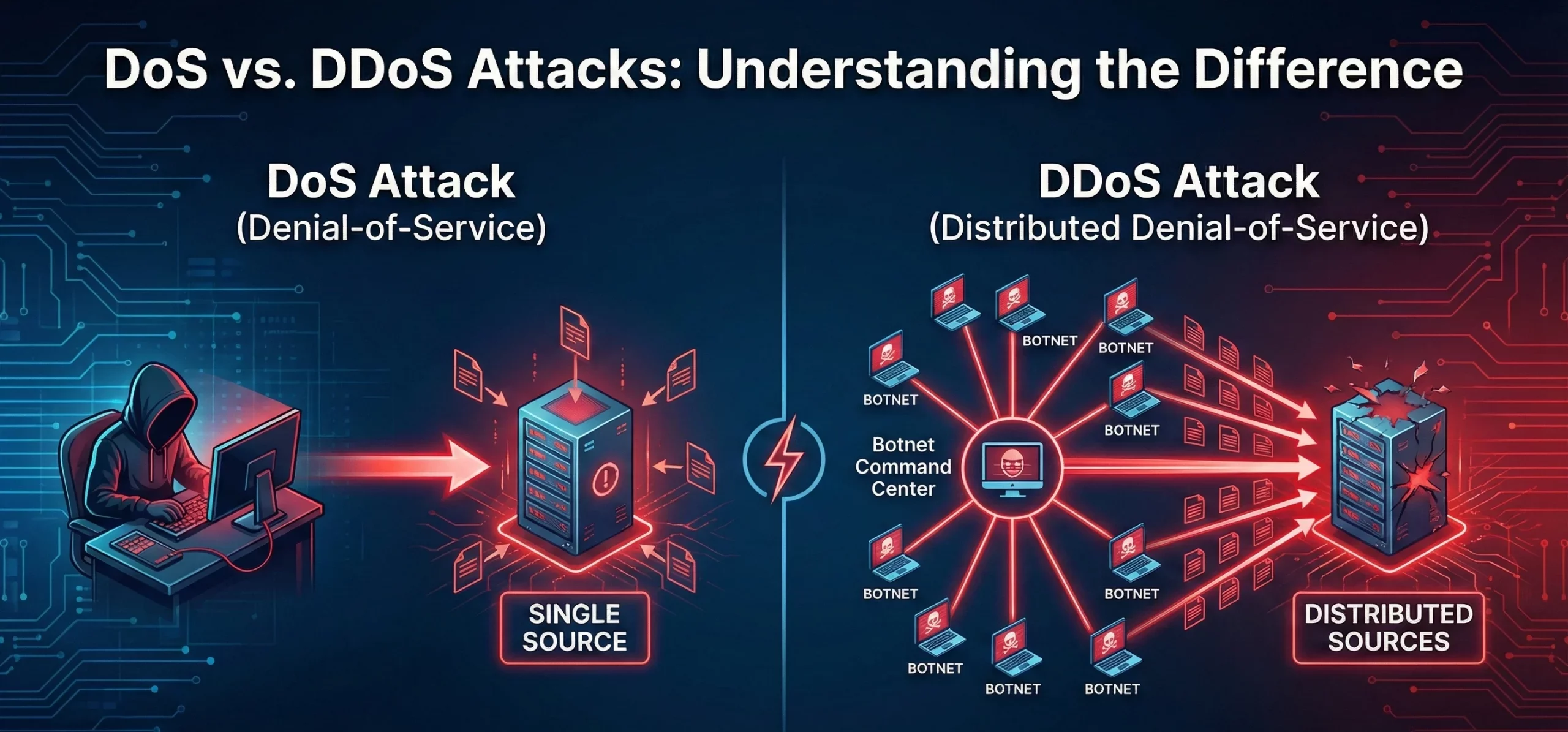
A Denial of Service (DoS) attack attempts to make a machine, network, or service unavailable to users by overwhelming traffic or requests. It typically originates from a single source.
Table of Contents
Toggle
A Distributed Denial of Service (DDoS) attack is similar in intent but involves multiple systems (often a botnet) targeting the victim simultaneously, making it harder to block or trace.
Key Characteristics of DoS & DDoS Attacks
DoS Attack
- Single source of traffic.
- Easier to mitigate due to identifiable origins.
- Lower scale and complexity compared to DDoS.
DDoS Attack
- Distributed across multiple compromised systems.
- Overwhelming scale and sophistication.
- Harder to block due to diverse traffic sources.
Commonly Used DoS/DDoS Attack Tools
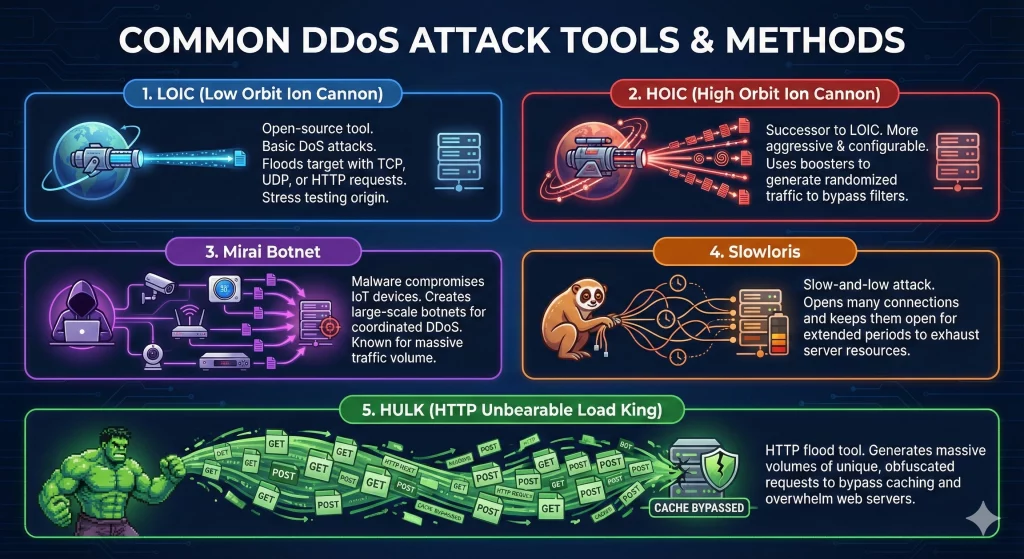
1. Low Orbit Ion Cannon (LOIC): Open-source tool used for basic DoS attacks.
2. HOIC (High Orbit Ion Cannon): Successor of LOIC, with a more aggressive and configurable attack mechanism.
3. Mirai Botnet: A malware that compromises IoT devices to launch large-scale DDoS attacks.
4. Slowloris: A tool that keeps connections open for extended periods, exhausting server resources.
5. HTTP Unbearable Load King (HULK): Generates large volumes of unique requests to overwhelm servers.
How Can I Defend Against DoS/DDoS Tools?
1. Invest in a Content Delivery Network (CDN): CDNs like Cloudflare or Akamai distribute traffic across multiple servers, mitigating attacks.
2. Use DDoS Protection Services: Services like AWS Shield and Arbor Networks detect and mitigate large-scale attacks.
3. Configure Firewalls and Rate Limits: Implement firewall rules to detect unusual traffic and rate-limiting to restrict requests from a single IP.
4. Regularly Update Systems: Keep software and systems patched to avoid vulnerabilities that attackers exploit.
5. Monitor Traffic Patterns: Use tools like Nagios or Zabbix to detect anomalies in traffic patterns early.
6. Implement Advanced Security Features: Deploy Web Application Firewalls (WAF) and Intrusion Prevention Systems (IPS) to filter malicious traffic.
DoS and DDoS Final Thought
DoS and DDoS attacks might sound like technical jargon, but understanding them is key to protecting your online world. These cyberthreats can disrupt businesses and services in a big way, but with the right tools and proactive measures, they can be managed effectively. Staying informed and prepared ensures that your digital life remains secure and running smoothly.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Read more
The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Read more
IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Read more